ZuSocial @Istanbul - Nov 14th Daily Roundup

1/ Intro to iExec
Guest: Yamine @Yamine
The challenge
In Marketing
User consent is often lacking
User privacy is compromised
User data is monetized by unknown parties
In Web3 Communication
Hard to reach users since they interact using wallets
The wallet represents the user's identity, thus privacy is important
What iExec proposes to tackle the problem
iExec's developer tools incl. DataProtector and Web3Mail.
DataProtector: Through DataProtector, users may allow apps to use their data without revealing the data itself, which is empowered by confidential computing.
Web3Mail: Enables an entity to email on Ethereum account holder without knowing her email address.
Developer rewards program
Currently, iExec also has the Developer Rewards Program of up to $1m funding to inspire developers to discover the protocol. There are 2 grants tracks to choose from: The fast track, and the advanced track.
Relevant link
iExec dev rewards program: https://iex.ec/grants/#:~:text=The%20Developer%20Rewards%20Program,available%20for%20more%20ambitious%20projects
Official site: https://iex.ec/
2/ Brand lab: Everybody can create an image that early adopters will love
Guest: Ira @eirenadesigns

What is brand?
Brand is a common opinion about your proudct, service or company in minds of people who interact with it.
Branding also has different stacks and layers including:
Rational knowledge: related to product & category
Sensory memory: related to identity
Personal (moral) judgements: related to value & mission
The methodology of design research
Research the soil: Design research helps to articulate and form the brand strategy
Product-market fit
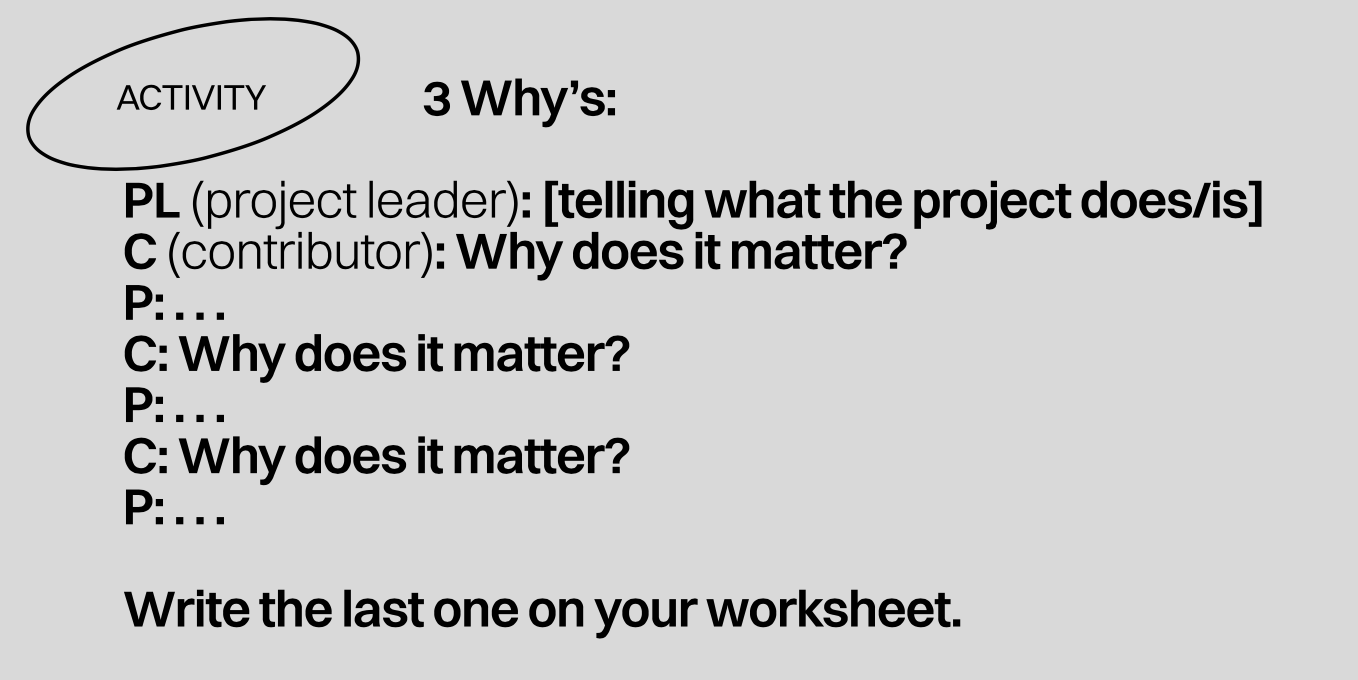
Customer personas: The "3 Whys" method
Competitor/ alternatives analysis
Landscape visual research
Relevant link:
Pick the right seeds: The right crossover between brand personality and visual anchors
The customer journey of meeting a new product/ project/ service is a reputation forming experience through brand visual identity, verbal identity & content strategy, user experience of onboarding, and customer experience. For the brand itself, it's a self-awareness process for personality building.
And visual design is the first thing exposed to customers/ audience, which needs the "North Star", i.e. Brand moodboard and visual tokens.
North star: Brand moodboard
Identifier: Logo
Tokens: Typefaces, Colors, Shapes, Visual heart
Identity PoC: Concepts and designs also need to be tested through Identity PoC to get feedback and iterate. The whole journey would include
Min viable brand
Brand position & design taboo
Brand personality
Moodboard + visual token
Identity PoC
First customer experience touchpoints
Relevant link:
3/ Autonomous Community Governance with Axiom
Guest: YJ and Roshan from Axiom @axiom_xyz

What is Axiom
Axiom is the ZK coprocessor for Ethereum. ZK coprocessors are a new class of blockchain infrastructure that allows smart contract developers to statelessly prove offchain computation over existing on-chain data.
Possibility with Axiom in Governance
Off-chain governance relies on multisigs to implement decisions on-chain, which leads to censorship of decisions the multisig opposes. With Axiom, the entire governance proces can be verified in a zk proof on-chain, which gives off-chain governance the same guarantees of on-chain governance without the costs.
Other potentials for governance within the community includes:
Transparent parameters for rewards
Reward the most dedicated members in the community
Autonomous governance
Where Axiom fits in
Axiom fits in:
Used to generate zk proofs of historical data
Have both on-chain and off-chain components
Used in conjunction with some method of getting the data, such as an indexer
Developer's contract can trustlessly use the data once the proof is generated
Reference link
Introducing Axiom: https://blog.axiom.xyz/introducing-axiom/
Docs: https://docs.axiom.xyz/
Official site: https://www.axiom.xyz/
4/ Intro to Solid
Guest: Jackson Morgan
The problem
Our personal data on different platforms, including social media and beyond, are siloed within each every of the platform and the ownership of the data is controlled by the platform.
What's Solid
Solid is an architecture that lets there be a utility for data. Solid lets people store their data securely in decentralized data stores called Pods (personal online datastore). Pods are like secure personal web servers for data.
Any kind of information can be stored in a Solid Pod
You control access to the data in your Pod. You decide what data to share and with whom (be it individuals, organizations, and/or applications). Furthermore, you can revoke access at any time
To store and access data in your Pod, applications use standard, open, and interoperable data formats and protocols.
Build a Solid app live!
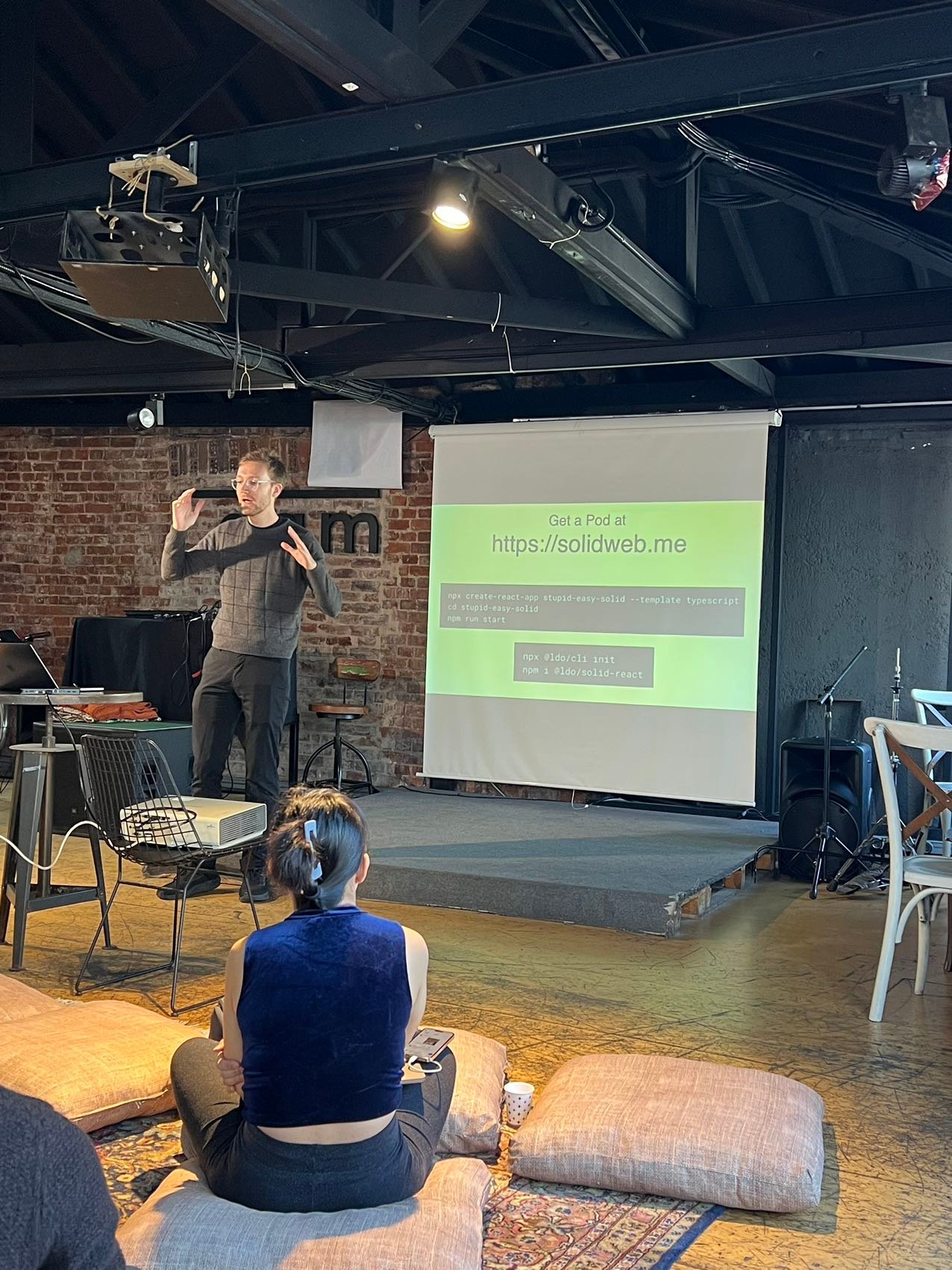
Reference link
Official site: https://solidproject.org/
5/ Mini Demo time @CryptoKitchens
Diverse ideas around decentralized social/ identity from our ZuSocial hackers with an amazing view in the background






喜欢我的作品吗?别忘了给予支持与赞赏,让我知道在创作的路上有你陪伴,一起延续这份热忱!